Zwell has posted an entry on Full Disclosure (FD) about a new version of Pangolin. This new version comes with an enhanced Oracle support
[…]
Sometimes we meet Oracle database when we do web sql injection testing. All we do is to dump some data in the db. But you know what? Actually, we can do more and more operation of it, just like:
1. Fast data dumping even cannot use union select
2. Dump server information like : db name, sid, real internet ip address, user list, user hash and so on.
3. Execute PL/SQL
4. Privilege escalation
5. Crack user password
6. Execute system command
7. Install oracle rootkit
8. and so many others
Maybe you could say it cannot execute multi-sql through a single query. Don’t worry. There is a demo at http://down2.nosec.org/swf/pangolin_oracle.html, you can watch it and learn a lot of things about Oracle sql injection.
[…]
Most of the stuff is not new… (at least not for me)
1. Fast data dumping even cannot use union select
==>usage of utl_http to get additional data. A faster way getting all results from multiple queries in a single query is described in a blog entry here.
utl_http is often revoked from public for security reasons. The usage of httpuritype is normally more reliable from the security perspective.
2. Dump server information:
==> via sys_context function. That’s standard Oracle functionality. Nothing special.
3. Execute PL/SQL
==> Pangolin is doing this via an exploit in dbms_export_extension. The bug in dbms_export_extension is old but this exploit was new for me…
4. Privilege escalation
==> I guess they are doing this via the exploit in dbms_export_extension
5. Crack (Oracle database) user password
==> Matrixay is doing this since several years.
6. Execute OS commands
==> several techniques (create table, dbms_scheduler, extproc, java, oracle text, plsql_native_9, plsql_native_10, set_events) are available to do this. Via PL/SQL this is easy to achieve…
7. Install Oracle rootkit
==> yeah. Simple via plsql
Maybe you could say it cannot execute multi-sql through a single query.
==> Stacked queries are not possible in Oracle. Correct me if I’m wrong. You are using a PL/SQL Injection vulnerability in a SQL function. This is a small but important difference.
BTW. :
The current version of Pangolin is using Openssl to crack Oracle passwords but not adding the Openssl license to pangolin. This is a license violation of the OpenSSL license…
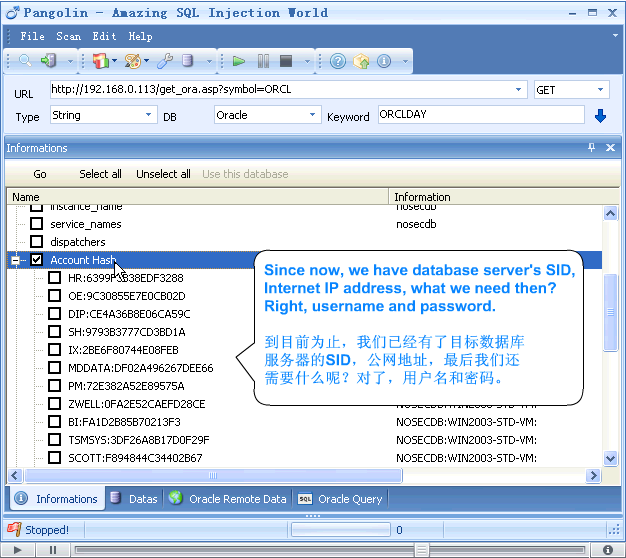
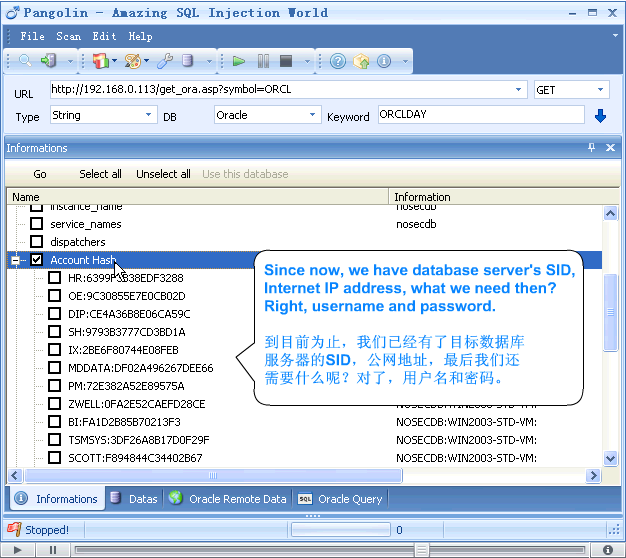
Here is a screen shot of Pangolin 2.0 (taken from the flash movie from the pangolin website):